Earth Kurma APT is actively targeting government and telecommunications orgs in Southeast Asia
Earth Kurma APT carried out a sophisticated campaign against government and telecommunications sectors in Southeast Asia. Trend Research exposed the Earth Kurma APT campaign targeting Southeast Asia’s government and telecom sectors. Threat actors use custom malware, rootkits, and cloud storage for espionage, credential theft, and data exfiltration, posing a high business risk with advanced evasion […]

Earth Kurma APT carried out a sophisticated campaign against government and telecommunications sectors in Southeast Asia.
Trend Research exposed the Earth Kurma APT campaign targeting Southeast Asia’s government and telecom sectors. Threat actors use custom malware, rootkits, and cloud storage for espionage, credential theft, and data exfiltration, posing a high business risk with advanced evasion techniques.
Earth Kurma particularly targeted the Philippines, Vietnam, Thailand, and Malaysia. Organizations face potential compromise of sensitive government and telecommunications data, the researchers speculate the attackers maintained prolonged, undetected access to their networks.
“Since June 2024, we uncovered a sophisticated APT campaign targeting multiple countries in Southeast Asia, including the Philippines, Vietnam, and Malaysia. We have named the threat actors behind this campaign “Earth Kurma.” Our analysis revealed that they primarily focused on government sectors, showing particular interest in data exfiltration.” reads the report published by Trend Micro. “Notably, this wave of attacks involved rootkits to maintain persistence and conceal their activities.”
The experts believe Earth Kurma is a new APT group targeting Southeast Asian government and telecom sectors since 2020, focusing on data theft via cloud services like Dropbox. The threat actor uses custom tools such as TESDAT, SIMPOBOXSPY and rootkits such as KRNRAT, MORIYA. Attribution overlaps exist but remain inconclusive.
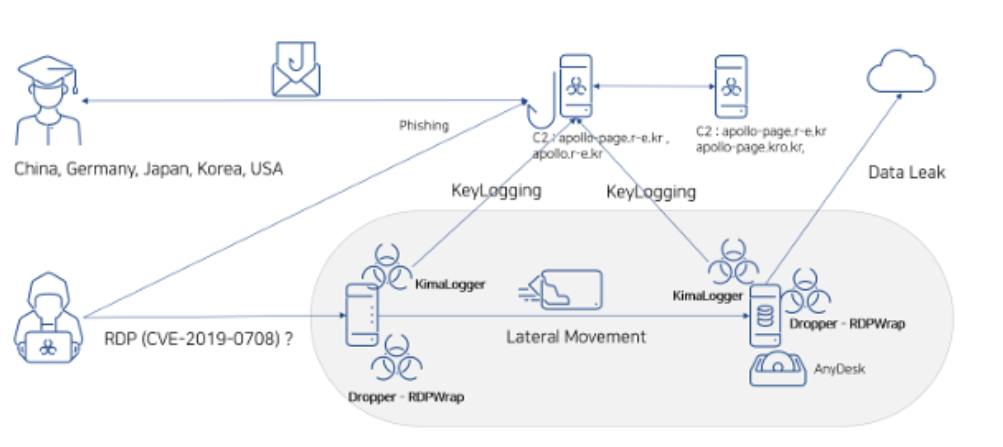
Below is the infection chain and malware used by the group:

Earth Kurma used tools like NBTSCAN, Ladon, FRPC, WMIHACKER, and ICMPinger for lateral movement, network scanning, and malware deployment. They also deployed KMLOG, a custom keylogger saving logs as disguised ZIP files. Attackers used WMI and SMB commands to move laterally and maintain stealth across victim infrastructures.
In the persistence stage, Earth Kurma deployed loaders like DUNLOADER, TESDAT, and DMLOADER to run payloads in memory and exfiltrate data via Dropbox and OneDrive. The attackers employed rootkits like KRNRAT and MORIYA to evade detection.
“As for attribution, we found overlaps between Earth Kurma’s tools and those of other known APT groups. The MORIYA rootkits in this campaign share the same code base as the ones used in Operation TunnelSnake, while SIMPOBOXSPY and the exfiltration script link closely to another APT group called ToddyCat.” continues the report. “However, differences in the attack patterns prevent us from conclusively attributing these campaigns and operations to the same threat actors. Hence, we named this new APT group “Earth Kurma.””
Between 2022 and 2024, Earth Kurma used loaders like DUNLOADER, TESDAT, and DMLOADER to deliver Cobalt Strike beacons. They later deployed MORIYA and KRNRAT rootkits to maintain persistence, hide activities, and exfiltrate data stealthily via memory injections and disguised cloud communications.
Attackers used a living-off-the-land binary called “syssetup.dll” to install the rootkits.
“Earth Kurma remains highly active, continuing to target countries around Southeast Asia. They have the capability to adapt to victim environments and maintain a stealthy presence.” concludes the report. “They can also reuse the same code base from previously identified campaigns to customize their toolsets, sometimes even utilizing the victim’s infrastructure to achieve their goals.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, APT)