Law enforcement dismantled the infrastructure behind Lumma Stealer MaaS
Microsoft found 394,000 Windows systems talking to Lumma stealer controllers, a victim pool that included global manufacturers. A US court order, with Europol and Japan’s JC3 dismantled the Lumma Stealer malware operation, seizing 2,300 domains used for command-and-control and blocking dark web markets offering the infostealer. A US court order, with Europol and Japan’s JC3, […]
Microsoft found 394,000 Windows systems talking to Lumma stealer controllers, a victim pool that included global manufacturers.
A US court order, with Europol and Japan’s JC3 dismantled the Lumma Stealer malware operation, seizing 2,300 domains used for command-and-control and blocking dark web markets offering the infostealer.
A US court order, with Europol and Japan’s JC3, dismantled Lumma Stealer’s infrastructure, seizing domains and control panels. Microsoft’s Digital Crimes Unit sinkholed over 1,300 domains to reroute victims to safe servers for analysis and cleanup.
“The Justice Department announced today the unsealing of two warrants authorizing the seizure of five internet domains used by malicious cyber actors to operate the LummaC2 information-stealing malware service.” reads the press release published by DoJ.
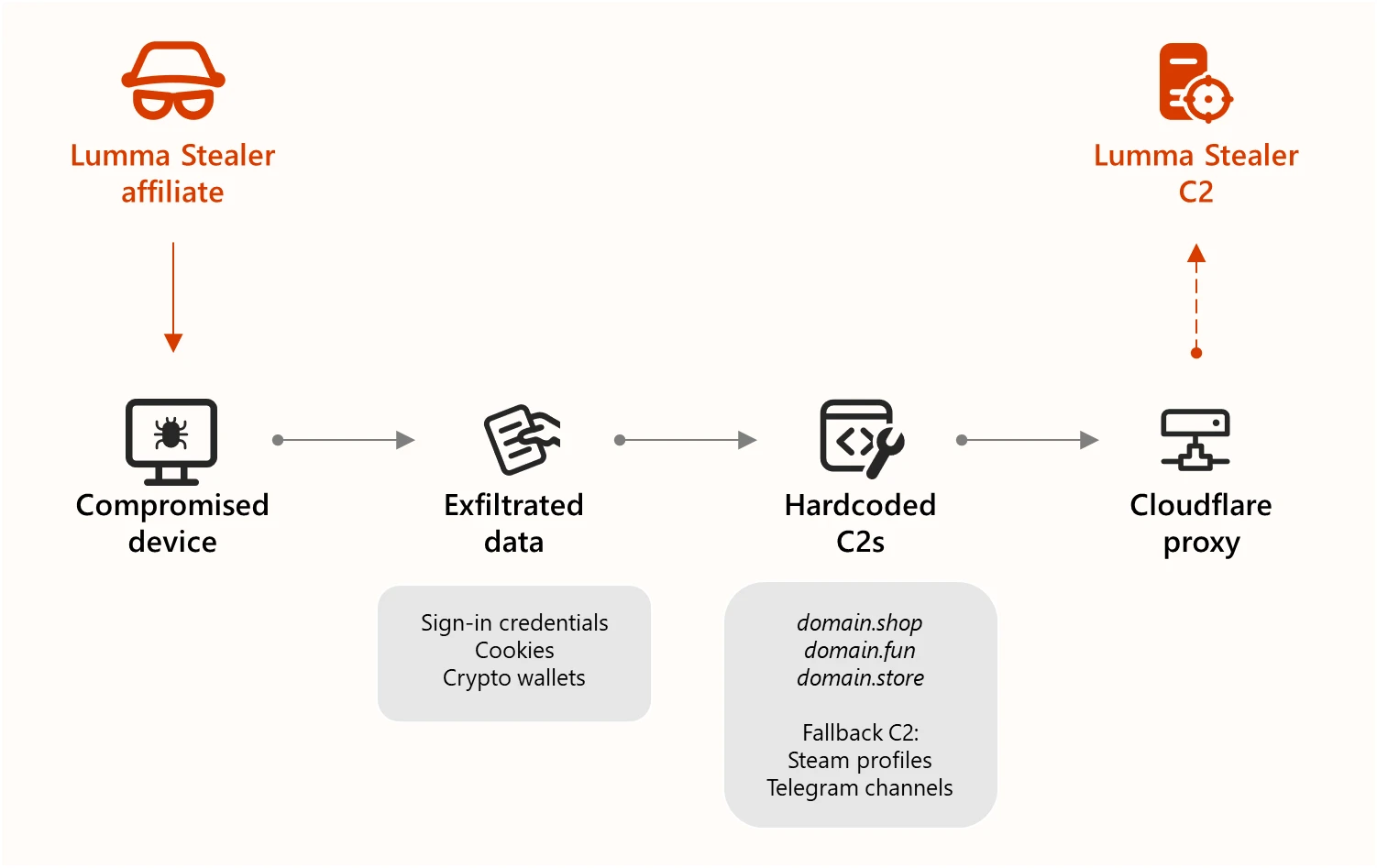
Lumma Stealer is a Malware-as-a-Service (MaaS) infostealer designed to steal sensitive data like passwords, credit card info, and crypto wallet keys. It infiltrates systems via phishing, malvertising, and malicious downloads. It can also deploy additional malware and evade detection.
The malware had infected over 394,000 Windows systems, including those of global manufacturers.
Microsoft observed Lumma Stealer’s rapid growth and sophistication as a MaaS used by financially motivated threat actors. Distributed via phishing, malvertising, and abuse of trusted platforms, Lumma targets browsers, wallets, and apps. Lumma’s flexibility and resilience highlight the evolving cybercrime landscape and the need for layered, collaborative defense efforts.
Microsoft tracks the developer of Lumma Stealer and its C2 infrastructure as threat actor Storm-2477. Ransomware groups like Octo Tempest, Storm-1607, Storm-1113, and Storm-1674 have used Lumma in their campaigns.
Lumma Stealer uses a layered C2 infrastructure with hardcoded tier 1 servers and fallback C2s via Telegram and Steam, all hidden behind Cloudflare. Telegram is prioritized, and Steam is used if others fail. Affiliates can pay for personal C2s. All communication is encrypted via HTTPS.

“Different types of obfuscation are applied to each set of C2 servers. For example, the hardcoded list of C2s, and including the Telegram fallback C2 URL are protected with ChaCha20 crypto, while the Steam profile fallback C2 URL is encrypted using custom stack-based crypto algorithm that can change on each version of Lumma malware.” states Microsoft. “We have identified up to six versions of Lumma Stealer, and while each of these versions focuses on improving techniques to evade antivirus detections, there are also several changes in the C2 communication protocol and formats such as the C2 domains, URI path, POST data, and others. The core Lumma malware stores the build date as part of the embedded configuration to keep track of improvements, but in our investigation, we tracked major changes using the labels “version 1” through “version 6”.”
The FBI and US CISA also released a joint advisory that includes tactics, techniques, and procedures (TTPs) associated with Lumma Stealer along with indicators of compromise (IOCs).
“Malware like LummaC2 is deployed to steal sensitive information such as user login credentials from millions of victims in order to facilitate a host of crimes, including fraudulent bank transfers and cryptocurrency theft,” said Matthew R. Galeotti, head of the Justice Department’s Criminal Division. “Today’s announcement demonstrates that the Justice Department is resolved to use court-ordered disruptions like this one to protect the public from the theft of their personal information and their assets. The Department is also committed to working with and appreciates the efforts of the private sector to safeguard the public from cybercrime.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, malware)