New botnet HTTPBot targets gaming and tech industries with surgical attacks
New botnet HTTPBot is targeting China’s gaming, tech, and education sectors, cybersecurity researchers warn. NSFOCUS cybersecurity discovered a new botnet called HTTPBot that has been used to target the gaming industry, technology firms, and educational institutions in China. HTTPBot is a Go-based botnet first detected in August 2024, however, its activity surged by April 2025. The botnet […]
New botnet HTTPBot is targeting China’s gaming, tech, and education sectors, cybersecurity researchers warn.
NSFOCUS cybersecurity discovered a new botnet called HTTPBot that has been used to target the gaming industry, technology firms, and educational institutions in China.
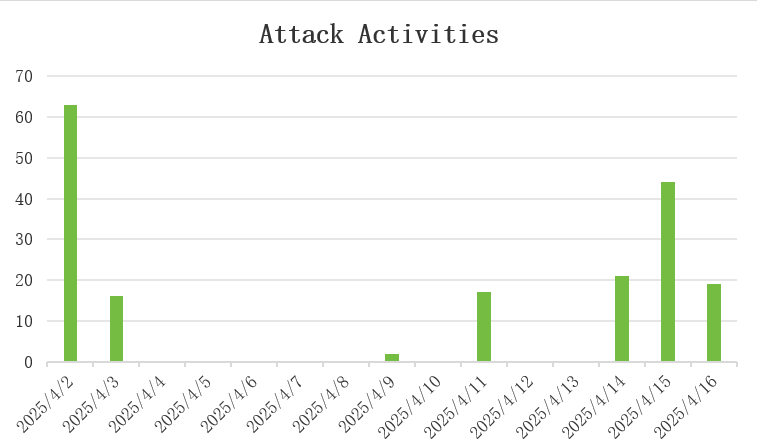
HTTPBot is a Go-based botnet first detected in August 2024, however, its activity surged by April 2025. The botnet was employed in highly targeted attacks, using a periodic, multi-stage strategy to launch continuous assaults on specific victims.
HTTPBot uses an “attack ID” for precise control and employs advanced DDoS tactics like HTTP Floods and obfuscation to bypass traditional detection methods.
“HTTPBot has taken a different approach by developing a range of HTTP-based attack methods to conduct transactional (business) DDoS attacks. Attackers can use these methods to precisely target high-value business interfaces and launch targeted saturation attacks on critical interfaces, such as game login and payment systems. This attack with “scalpel-like” precision poses a systemic threat to industries that rely on real-time interaction.” reads the report published by NSFOCUS. “HTTPBot marks a paradigm shift in DDoS attacks, moving from “indiscriminate traffic suppression” to “high-precision business strangulation.”
Since early April 2025, the botnet has issued over 200 attack commands, with activity spread across all hours of the day.
The researchers pointed out that the botnet supports 7 built-in DDoS attack methods, all of which are http types. The attack methods mainly used in its attacks include http_fp, http_auto and HTTP.
“The above attacks covered more than 80 independent targets, mainly in the domestic gaming industry, but also technology companies, educational institutions and tourist attractions.” continues the report. “Attackers usually launch multiple rounds of attacks on the same target in different time periods, with clear targets.”
The malware hides its GUI to evade detection and ensures persistence by adding itself to the Windows startup registry.
The bot communicates with its server via a streamlined process using an “attack ID” for precise control. It supports 7 HTTP-based DDoS methods, configurable with parameters like target, duration, and method. Below are attacks methods detailed by the researchers:
- BrowserAttack: Launches hidden Chrome instances to simulate real user behavior and deplete server resources.
- HttpAutoAttack: Utilizes cookies to mimic legitimate session behavior with high accuracy.
- HttpFpDlAttack: Leverages the HTTP/2 protocol to overload server CPUs by triggering large response payloads.
- WebSocketAttack: Establishes connections using “ws://” and “wss://” protocols to exploit WebSocket communication.
- PostAttack: Conducts attacks by forcing the use of HTTP POST requests.
- CookieAttack: Enhances BrowserAttack with advanced cookie handling to further imitate authentic web interactions.
The malware bypasses detection using Base64 encoding, dynamic URLs, and simulates human behavior. Some attacks require Windows version greater than 8, showcasing advanced evasion and control techniques.
“DDoS Botnet families tend to congregate on Linux and IoT platforms. However, the HTTPBot Botnet family has specifically targeted the Windows platform. In just a few months, it has emerged as a significant threat that cannot be ignored on the Windows platform.” concludes the report.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, botnet)