Russia-linked APT28 targets western logistics entities and technology firms
CISA warns Russia-linked group APT28 is targeting Western logistics and tech firms aiding Ukraine, posing an elevated threat to supply chains Russia-linked cyberespionage group APT28 intensifies its operations against Western logistics and technology companies moving supplies into Ukraine, US CISA warns. The APT28 group (aka Fancy Bear, Pawn Storm, Sofacy Group, Sednit, BlueDelta, and STRONTIUM) has been active since at least 2007 and it […]
CISA warns Russia-linked group APT28 is targeting Western logistics and tech firms aiding Ukraine, posing an elevated threat to supply chains
Russia-linked cyberespionage group APT28 intensifies its operations against Western logistics and technology companies moving supplies into Ukraine, US CISA warns.
The APT28 group (aka Fancy Bear, Pawn Storm, Sofacy Group, Sednit, BlueDelta, and STRONTIUM) has been active since at least 2007 and it has targeted governments, militaries, and security organizations worldwide. The group was involved also in the string of attacks that targeted 2016 Presidential election.
The group operates out of military unity 26165 of the Russian General Staff Main Intelligence Directorate (GRU) 85th Main Special Service Center (GTsSS).
“This joint cybersecurity advisory (CSA) highlights a Russian state-sponsored cyber campaign targeting Western logistics entities and technology companies. This includes those involved in the coordination, transport, and delivery of foreign assistance to Ukraine. Since 2022, Western logistics entities and IT companies have faced an elevated risk of targeting by the Russian General Staff Main Intelligence Directorate (GRU) 85th Main Special Service Center (85th GTsSS), military unit 26165—tracked in the cybersecurity community under several names (see “Cybersecurity Industry Tracking”).” reads the joint alert. “The actors’ cyber espionage-oriented campaign, targeting technology companies and logistics entities, uses a mix of previously disclosed tactics, techniques, and procedures (TTPs). The authoring agencies expect similar targeting and TTP use to continue.”
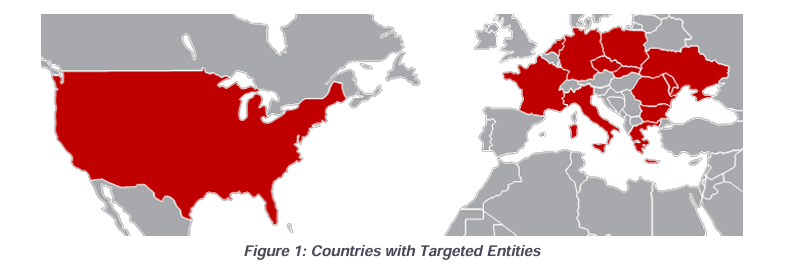
Russian GRU Unit 26165 has targeted dozens of Western logistics and tech firms tied to Ukraine aid, including defense, maritime, air, and rail sectors across NATO nations and Ukraine. They exploited business ties to expand access, even probing ICS makers for railway systems. Targets span 13 countries, including the U.S., Germany, and France.

APT28 used various methods for initial access, including brute-force attacks, spear-phishing, and exploiting known vulnerabilities in Outlook, Roundcube, WinRAR, VPNs, and SOHO devices. They also used compromised nearby devices to proxy attacks and evade detection.
GRU Unit 26165 used spearphishing with fake login pages hosted on compromised devices or free services. Attackers sent emails mimicking government/cloud providers, often in the target language, and used lures like legit documents. Some campaigns bypassed MFA and used IP checks, redirectors, and delivered malware.
GRU Unit 26165 exploited CVE-2023-23397 in Outlook to steal NTLM hashes via fake calendar invites and used Roundcube CVEs to access emails and run commands. Since fall 2023, they also leveraged a WinRAR flaw (CVE-2023-38831) to execute code via malicious archives sent through emails or embedded links.
After initial access, APT 28 conducted reconnaissance on key personnel, cybersecurity teams, and partners. The experts observed the group using tools like Impacket, PsExec, RDP, and Certipy for lateral movement and Active Directory data exfiltration. The actors harvested credentials, manipulated mailbox permissions, and accessed sensitive shipment data. Threat actors also used voice phishing to target privileged accounts.
The Russia-linked group used malicious code for access, persistence, and data theft, deploying custom malware like HEADLACE and MASEPIE. They used DLL hijacking, scheduled tasks, run keys, and malicious shortcuts to maintain access. Experts warned that attackers can use other malware like OCEANMAP and STEELHOOK in cyber operations against logistics and IT sectors.
The threat actors exfiltrated data using PowerShell, APIs (EWS/IMAP), and periodic queries, leveraging local infrastructure to evade detection. Attackers also targeted IP cameras near Ukrainian borders and military sites via RTSP, using default/brute-forced credentials to access live feeds. This campaign helped monitor aid and material movement into Ukraine.
The alert includes general and detailed security mitigations.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Russia)





![Nomad levels up its best-selling charger with new 100W slim adapter [Hands-on]](https://i0.wp.com/9to5mac.com/wp-content/uploads/sites/6/2025/05/Banner_1_944db232-8ae3-479c-a10b-9ba6c985b7b2.jpeg?resize=1200%2C628&quality=82&strip=all&ssl=1)
